New name, new modules, new approach to security awareness e-learning. Infosequre has spent the last stretch of time taking a hard look at its vision and approach to teaching people. Now, at the end of this tunnel of transformation, a new picture emerged: one that is more aligned with the company’s core beliefs and with the current climate of the digital landscape.
Eva van Eijden is an e-learning developer working for Infosequre, and was part of the team that brought the new ideas, concepts and techniques to life, so I asked her if she could shed some light on the process and the result of this transformation.
What triggered this revamp of style and substance within the company? Is the approach completely new in a way that you totally reformed the e-learning material?
The field of e-learning is ever-changing and not what it was a couple of years ago anymore. Gamification, interactivity and the experience of the trainee have become an integral part of online learning. Even though our security awareness e-learning material has always included interactive elements, we thought it was time for a drastic change in our approach to making e-learning material.
So how did you make it happen? I assume this meant focusing on certain elements to really drive the point home. What would you say those core elements are?
Our past year revolved around forming a new philosophy that is all about incorporating elements of gamification and story-based learning. This means that the experience of the employee is central and that interactivity between employee and e-learning material is key. We want to take employees on a journey in which they have a mission to complete or a mystery to uncover. By using a strong storyline, interactive videos and engaging exercises we implement this new approach in our new e-learning material. From now on, this is our starting point.
The experience of the employee is central and interactivity between employee and e-learning material is key.
A lot of sources cite interactivity and immersiveness as central factors to pull in the viewer, or, in your case, the learner. But how does that work in practice?
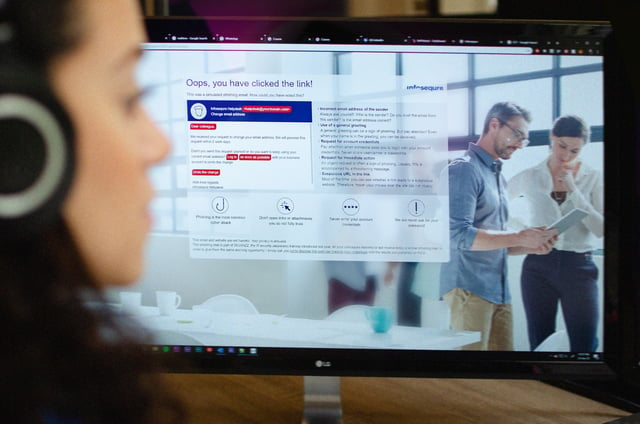
A new approach is not the only thing we’ve been creating. The first 2 security awareness e-learning modules that follow this approach have just been released. The first module is about phishing and discusses all the necessary subjects: phishing via different media (email, SMS and social media), what information cybercriminals can find on the internet and use in their attacks, the signs of phishing, how to check if a link is suspicious, and what to do when you think you’ve received a phishingmail.
However, the module takes a whole different perspective than you’re used to: YOU are the one planning a phishing attack, doing the research on your victims, writing a convincing phishingmail and waiting for your first victim to click on the link. Will you succeed or are your victims smarter than you thought?
The second module that we’ve reinvented is about mobile devices. In this module you’ve just started at a new job, but when you meet your colleagues for the very first time something is amiss. Information about a new project got leaked and is now all over the internet. You talk to every team member to find out how they handle their mobile devices to find out if they might have made some errors lately that could have caused the leak.
During this quest we discuss downloading apps, keeping software up to date, what to do when you’re working away from the office and which measures to take to protect the information on your devices against loss or theft. Employees can use the information in this module not only in their business life, but also to keep their personal devices safe. A real win-win!
Thanks Eva! If you’d like to learn more or even have a taste of our new modules, head over to our e-learning page to get all the details and request a demo.